Network Address Translation
Unit Goals
Why NAT?
There aren’t enough IPv4 addresses to go around.
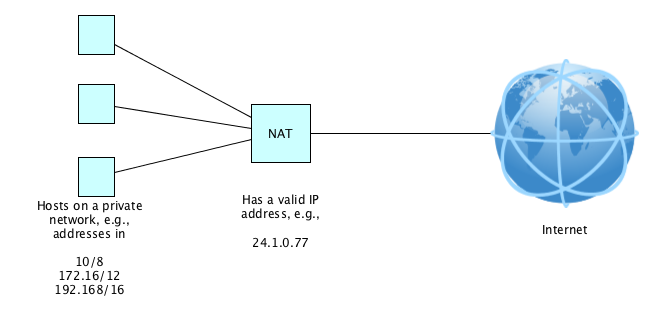
NAT, or network address translation, also known as “transparent proxying” or “IP Address Overloading” or “IP Masquerading” is a way to keep IPv4 alive. Or to at least hide your real IP address.
Let’s learn by example, assuming the normal use case of a private IP network.
How NAT Works, By Example
Here’s a typical scenario:
Suppose a host on this private network, 192.168.1.5, from an application on port 9266, wants to send a TCP packet to 207.44.189.183 on port 8053.
It creates and sends off a TCP packet to the NAT box like this:
| Source Port | 9266 |
| Dest Port | 8053 |
| • • • | |
| Source IP | 192.168.1.5 |
| Dest IP | 207.44.189.183 |
Note the trickery!The host is sending a TCP segment to a host on its own network such that the destination in the TCP segment differs from the destination in the IP datagram that wraps the TCP segment. It’s all good. But pretty cool, right?
The NAT box maintains a mapping of (its own) port numbers to (IP, Port) pairs. So, on receiving the above segment, it makes a new entry in its table. Let’s say the next free slot in the table was at 7969. It makes an entry like so:
| 7966 | 192.168.18.33, 2409 |
| 7967 | 192.168.3.150, 1511 |
| 7968 | 192.168.11.101, 8080 |
| 7969 | 192.168.1.5, 9266 |
Then the NAT rewrites the TCP segment into:
| Source Port | 7969 |
| Dest Port | 8053 |
| • • • | |
| Source IP | 24.1.0.77 |
| Dest IP | 207.44.189.183 |
and sends it on its way.
The remote machine sees the segment as coming from the NAT box, 24.1.0.77 at port 7969. Therefore, when it replies, it sends a segment like:
| Dest Port | 7969 |
| • • • | |
| Source IP | 207.44.189.183 |
| Dest IP | 24.1.0.77 |
The NAT recognizes this segment as coming from the outside addressed to port 7969. So it does a lookup in the translation table and rewrites the segment to:
| Dest Port | 9266 |
| • • • | |
| Source IP | 207.44.189.183 |
| Dest IP | 192.168.1.5 |
and sends it to the right host on its own network.
Summary
We’ve covered:
- Why we need NAT
- How NAT works